7 Top E-Commerce Solutions from Jain Software
In Official Blog, Business, Digital Marketing, Marketing, Services on Perfection, Tech-BLOG
E-Commerce Solutions
In the present era of digital economy, a firm cannot afford to be devoid of an e-commerce platform for the purpose of achieving increased competitiveness, as well as broadening its market reach and improving the quality of its offered services to the customer. Jain Software as an IT solutions provider presents a wide range of e-commerce solutions matched to the needs of companies of different types. The services Jain Software offers leverage the company’s goal of supporting all aspects of an e-commerce business from user experience to analytics. In this blog, you will learn about the 7 best e-commerce solutions from Jain Software and how they can help your business.
1. Software as a Service e-commerce Platforms
Each business is distinct, and, therefore, require different e-commerce solutions. Jain Software helps you develop unique, brand specific e-commerce solutions that automatically support your business objectives.
Features:
- Tailored Design: Ability to set customized themes and layout to fit your brand image.
- Scalability: Solutions that are scalable, so that they can handle an increasing number of products for sale and a rising clientele.
- Responsive Design: Responsive designs for better user experience when shopping via computers, tablets and mobile phones.
- Multi-Language and Multi-Currency Support: Allowing organizations to meet the needs of customers around the world.
Benefits:
An adjustable platform allows for the development of a arrival of environment that is satisfying and will help prevent customers from seeking a different shopping experience.
2. Inventory Management Systems
Inventory control plays an important aspect in every and ecommerce business venture. The systems from Jain Software also help in real time monitoring of the inventory thus minimizing situations where a company sells a product that it does not have in its stock or in the other extreme, when it lacks products it has sold.
Features:
- Real-Time Updates: Scalable stock levels tracking in real time.
- Automatic Restocking Alerts: Alerts that inform the user that the stock of the products is low.
- Integration with Sales Channels: In effect, the inventory should be synchronized to some of these platforms as the Amazon, Flipkart and your website.
- Batch Tracking: Batching the products would facilitate quality assurance as a way of dealing with quality control.
Benefits:
Smooth flow of inventory is noteworthy as it leads to cost-effective functioning, and maximum convenience for customers due to guaranteed timely availability of goods.
3. Secure Payment Gateways
At Jain Software, we incorporate respected, secure, and flexible payment gateways so that clients’ trust in the convenience of such transactions is well placed.
Features:
- Multiple Payment Options: Card/net payments, device/net payments, bank transfer, credit/debit cards, digital wallets, and cash on delivery.
- Encryption and Security: Strong security measures to ensure customer’s information privacy.
- One-Click Payments: Savings made by avoiding entry of frequent payment methods and the time it would have taken to enter them repeatedly.
- Multi-Currency Processing: Painless international dealings.
Benefits:
Payments must be safe also to build customer trust while it has the same effect of reducing cart abandonment rates, thereby improving the sale.
4. Convenience for Users when Shopping
Effective e-commerce interface is another aspect of ensuring that the progress of e- business. Jain Software creates easy to navigate platforms and good shopping experience is of utmost importance to the company.
Features:
- Search and Filter Options: Search options to narrow down the criterion in order to enable the quick identification by the customers.
- Personalized Recommendations: AI part for recommending products based on browser’s list and his/her previous purchase.
- Quick Checkout: Optimized complex call-to-action paradigms on multiple purchasing steps to decrease customer efforts.
- Wishlist and Save-for-Later Features: Encouraging future purchases.
Benefits:
Improve user experience makes bounce rates lower, the average time spent on the platform higher and brings back customers for more.
5. Datamining and Business Intelligence System
Knowledge of the customers’ behavior and trends in the market has significant roles in decision making. Jain Software provides complete reporting solutions for e-Business Companies.
Features:
- Customer Insights: Information about users such as; user demographics, user spending behavior, and user preferences.
- Sales Reports: Information regarding daily, weekly, monthly, annual revenues, best selling products, and variations in sales per season etc.
- Traffic Analysis: More information on how customers locate the store.
- Conversion Tracking: Knowing which campaigns are responsible for sales.
Benefits:
Using data as a tool gives the company a way of identifying the right audience to market to, ways of marketing and even a better way of getting the return on investment.
6. Integrated Marketing Tools
Marketing is the single most important aspect of any e-commerce organization. Jain Software offers ticketing to assist you in communicating to your target market.
Features:
- Email Campaigns: Incoming emails for cart abandonment, sales, and subscription.
- SEO Optimization: Furthermore, they have worked to incorporate other built-in tools to enhance its search engine rank.
- Social Media Integration: Post products on these social media applications as it shares a product instantly on an individual’s Instagram, Facebook, Twitter, etc.
- Discount and Coupon Management: Manage and monitor different promotional activities.
Benefits:
Through marketing tools, the identified enterprise can target more consumers, make them aware of its products, and convert them into consumers.
https://www.jain.software/3-key-website-with-jain-software
7. Customer Relationship Management (CRM)
Most importantly, customer relationship has been regarded as a key determinant for long term sustainability. CRM, services developed by Jain Software are aimed at enhanced customer relations and loyalty.
Features:
- Centralized Customer Data: Customer details should be properly stored and managed to observe health standard measures.
- Support Ticketing System: Build the treatment of customer inquiries and complaints as a priority on the company’s guideline.
- Loyalty Programs: Bonus is another method that should be given to frequent consumers.
- Feedback Integration: Inform potential and current customers in order to enhance services delivery.
Benefits:
A good CRM system simply blooms the trust with the customers and makes them loyal in such a way that they prefer to buy the products alone.
Why Jain Software for E-Commerce Solutions
- Expertise: Over the years, Jain Software has accumulated sufficient experience to design solutions suitable to various industries.
- Customizability: All these services can be as tailored to suit your needs as much as possible.
- Affordability: Reasonable prices guarantee the achievement of the best returns on investment.
- End-to-End Services: Jain Software is always with you from the development phase up to the stage of maintenance.
- Cutting-Edge Technology: At Dot Trends, employing the trending technologies helps keep your e-commerce platform current.
Real-Life Success Stories
Case Study 1: Strategies to Change a Retail Business
An organization operating a conventional physical storefront contracted Jain Software to design its web store. By integrating Jain Software’s web based selling platform and full complement of marketing tools, the business gained a forty percent increase in selling within the initial quarter.
Case Study 2: Improving on the aspect of Inventory control
A medium-sized e-commerce firm was experiencing problems with poor stock control. In Jain Software case, using of real-time inventory tracking minimized the stock outs by 30%, enhancing customer satisfaction situation a lot.
Case Study 3: Boosting Customer Retention
This is a good example that shows how one of the beauty brands united CRM and its loyalty programs with the help of outsourcing at Jain Software, and received a 25 per cent increase in repeat customers in the space of six months.
Conclusion
Jain Software offers cutting edge internet solutions especially for the e commerce companies. From open mobility systems, payment security services to sales boosting analytics and customer relation management tools, these solutions offer all that is required to operate a viable e-commerce outlet.
Regardless of your situation, whether you’re a new startup planning to create an online store for the first time, or a large firm eager to grow and expand your online presence, Jain has the capacity and the resources to support your growth.
Let Jain Software help put your e-commerce dream into practice—call us now to begin!
Follow Social Media :
https://www.facebook.com/jainsoftware/
https://www.instagram.com/jainsoftware/
https://www.linkedin.com/company/jainsoftware
https://x.com/jainsoftware







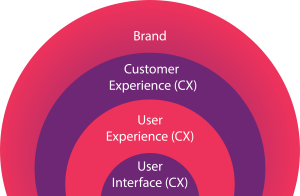 In the ever-evolving digital sphere, where user expectations are evolving at warp speed, the significance of a seamless and captivating user experience (UX) cannot be overstated. A well-crafted User Interface (UI) working in tandem with an intuitive User Experience (UX) has the potential to differentiate your business and drive heightened customer satisfaction, engagement, and conversions. In this blog, we embark on a journey into the realm of UI/UX services, exploring their pivotal role, myriad benefits, and how they can revolutionize your online presence.
In the ever-evolving digital sphere, where user expectations are evolving at warp speed, the significance of a seamless and captivating user experience (UX) cannot be overstated. A well-crafted User Interface (UI) working in tandem with an intuitive User Experience (UX) has the potential to differentiate your business and drive heightened customer satisfaction, engagement, and conversions. In this blog, we embark on a journey into the realm of UI/UX services, exploring their pivotal role, myriad benefits, and how they can revolutionize your online presence.